Airminded was down for a couple of days recently, and it now has a new look. The reason for this is that it was hacked, and nuking the entire site from orbit was the only way to be sure.
To be more specific, I noticed last week that Google searches for Airminded were throwing up some odd results, with words and links that no real person has ever typed on this blog appearing next to the more expected ones. But when I checked the posts in question, they looked fine. So, spoofing my browser’s user agent, I was able to see Airminded as Googlebot saw it, and it looked something like this:
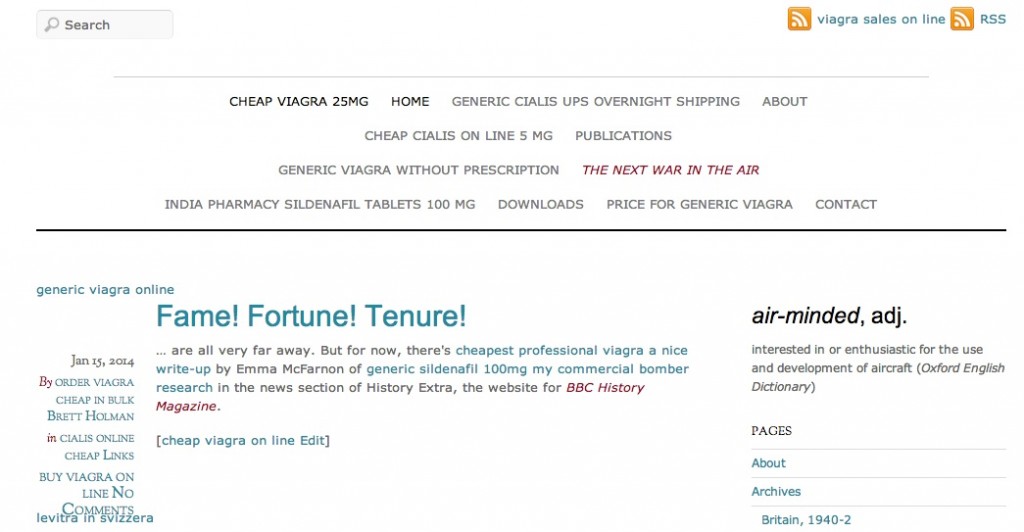
So Airminded was cloaked; this is known as a Pharma (for obvious reasons) hack. It’s quite insidious. Because the spam links are visible only to Google, they can easily go undetected for a long time. That might not sound like a problem, except that eventually Google decides that your site is full of spam and your PageRank starts to suffer and you disappear from searches.
This actually happened once before, a couple of years ago, and it was relatively easy to fix then. You just need to work out which PHP files have been modified or uploaded by the hackers and fix them, and also close whatever security hole they got in through. So I started poking around and quickly found a hacked file in one of the WordPress plugins, with its tell-tale base64 payload. I replaced it with a clean version and checked the Googlebot view of my site again, but the spam links were still there. Found another hacked file, fixed it, same result. Found yet another… and another… and another. Eventually it became clear that Airminded was thoroughly compromised, and that it would be easier just to delete all the files and reinstall WordPress, themes, and plugins from scratch, and the content and (most importantly!) the MySQL database from a backup. And hope that the database itself hadn’t been compromised. Otherwise, I could spend a week going over all the files on the site and still never be certain that I’d removed every backdoor.
But the problem now was that I didn’t know how the original compromise had occurred, so if I restored Airminded’s files to the way they had been last week or even a couple of months ago (which is when the hackers first got in), it would just be hacked again. With the help of WPScan, I think I’ve found that the weak link was in the theme, Elemin. A vulnerability in Elemin was disclosed shortly before Airminded was hacked, and the theme was definitely being used to upload files. Elemin’s developers actually fixed the vulnerability very quickly, but didn’t (as far as I know) make any effort to contact users to tell them about the problem. Since I paid for this theme, I’m not really happy about that, and decided it was time to ditch Elemin for Tiny Forge.
So, anyway, I’ve reinstalled WordPress and the old plugins (or switched to better, or least non-abandoned, plugins), installed, configured and styled Tiny Forge, restored the images and so on, and imported a backup of the database (which, luckily, appears to be okay). No data has been lost, though there are still a few things I need to fix and tweak. And Airminded is no longer cloaked, and scans find no problems. Fingers crossed.
![]() This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.
Permissions beyond the scope of this license may be available at http://airminded.org/copyright/.
This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.
Permissions beyond the scope of this license may be available at http://airminded.org/copyright/.



Area bombing!
Nabs! That’s a much more apposite metaphor for this blog, so it’s a shame I didn’t think of it. On the other hand: Aliens.
The problem with area bombing is that you end up dropping sticks of small bombs that can’t really devastate structures.
If only there were some kind of explosive that transcended the limits of chemistry. Then, when we bombed a site, we could be sure.
Welcome back… again!
Yeah, so, it turns out that ‘entire’ a very important word in this phrase. One part of the old site I didn’t rebuild was another WordPress blog called scareships which wasn’t being used as a blog but as a chronicle of the 1909 and 1913 phantom airship waves. I checked it and it wasn’t affected by the pharma hack itself, so I left it alone. However it turns out that the hacker had installed at least one backdoor in scareships and used that to get back into Airminded itself. This was made possible by the way I had scareships running in a subdirectory of Airminded, rather than on its own domain. So, I removed scareships and rebuilt Airminded again (it gets easier with practice!) I could put scareships back in a domain (or subdomain, anyway) of its own, but I probably won’t bother: the 1909 and 1913 phantom airship postblogging exercises provide much of the same information and a lot more besides.
Nice gravatar, Jason!